Morphing Attacks
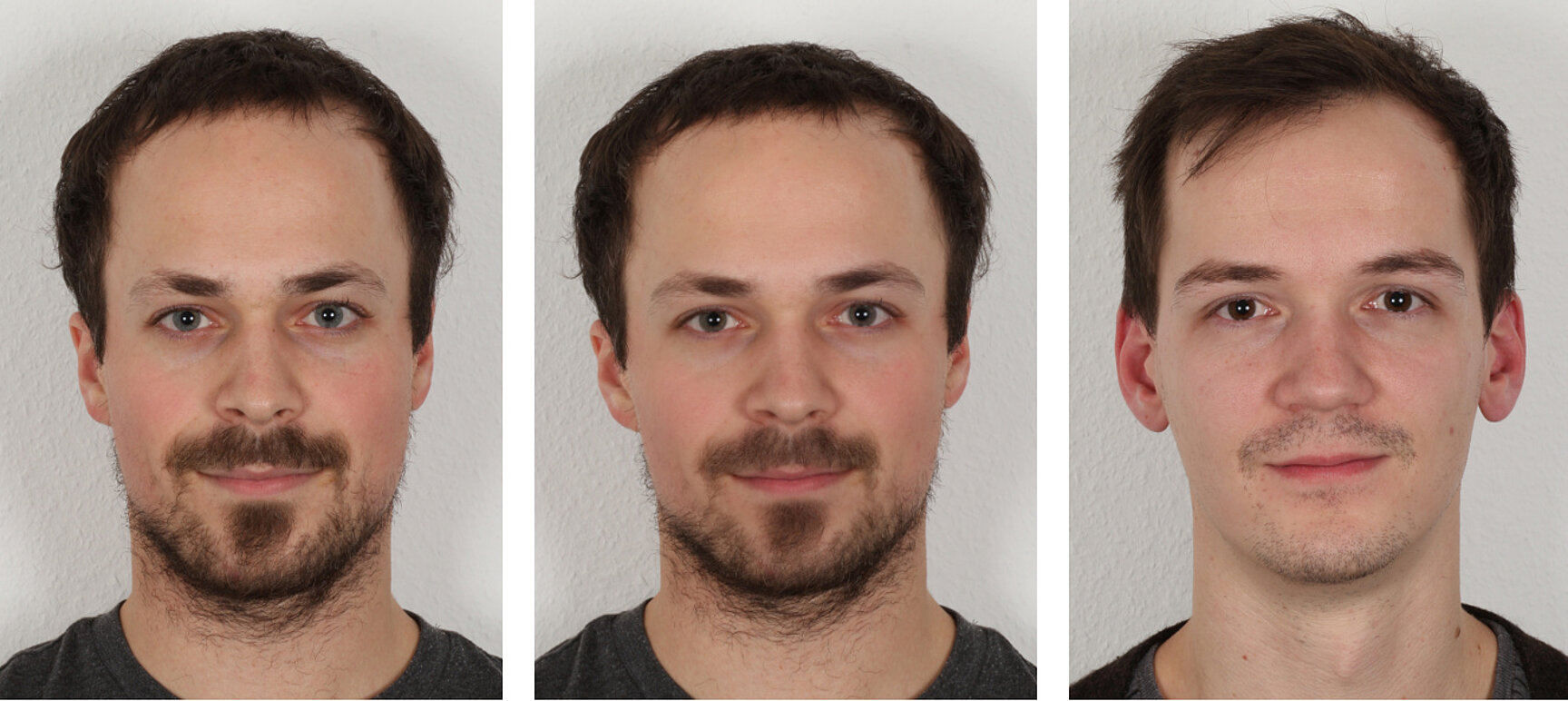
Identification tasks with identity cards, passports and visa are often performed automatically by biometric face recognition systems. Criminals can trick these systems, such that two people can use the same passport for authentication. This attack (morphing attack) is performed by fusing two face images to a synthetic face image that contains characteristics of both people. Using this image on a passport, both people are authenticated by a biometric face recognition system.
Participation in international Benchmark
We participated in the Face Analysis Technology Evaluation MORPH of by the National Institute of Standards and Technology (NIST) with our deep learning-based face morphing detector. Our detector, which operates using single-image analysis - meaning no reference image of the subject is required - demonstrated high performance in several categories.
See the results at: https://pages.nist.gov/frvt/html/frvt_morph.html Our detectors are named hhi_001 and hhi_002.
Morphed Face Images Datasets
We provide a dataset of morphed face images for interested researchers. The dataset was generated using advanced face morphing methods that address the limitations of the common key-point-based face morphing pipeline. The methods include an improved alignment process to avoid ghosting artifacts and use Neural Morph Enhancement to restore the sharpness of the original images, effectively removing the morphing-typical blurriness.
For further information, see: https://cvg.hhi.fraunhofer.de/FaceMorphData.htm
Improved Alignment of Face Images
Automatic generation of morphed face images often produces ghosting artifacts due to poorly aligned structures in the input images. Manual processing can mitigate these artifacts, but is not feasible for the generation of large datasets for training and evaluating morphing attack detectors. We proposed a method for automatic prevention of ghosting artifacts based on a pixel-wise alignment during morph generation.

Deep Morphing Detection
To generate a face morph, we align two face images, such that each facial feature (e.g. left corner of the right eye) is at the same position in both images. Since the haircut and the ears are difficult or even impossible to align and usually ignored by commercial facial recognition systems, we blend only the face region and stitch it into one of the aligned input images. The transitions are calculated individually for different frequency bands and an optimal stitch line is estimated.
In order to decide whether a face image is authentic or crated by a morphing algorithm, we trained deep convolutional neural networks on morphed and original face images. Since we focus on semantic image content, like highlights in the eyes or the shape and appearance of facial features to determine the authenticity of a face image, we applied several preprocessing steps on our training data to remove sensor or camera specific information. In addition to a decision about the authenticity of an image, we are also interested in a reason for decision. For this purpose, we analyze the regions in the face image that were relevant for the networks decision using the Layer-wise Relevance Propagation (LRP) Toolbox.
Transparent Decisions by Precise Localization of Traces of Forgery
In addition to our face morphing detector that provides only a decision and a confidence score, we developed a system to precisely highlight traces of forgery in morphed face images. In order to develop such a system, we started with an in-depth analysis of our DNN-based face morphing detectors and discovered that a naïve training of these detectors has some drawbacks. The naively trained DNNs tend to focus mostly on the eyes and pay little attention to traces of forgery in other regions of the face. In order to build a tool that can detect and localize traces of forgery in all parts of the face, this can be a problem and a detector that is sensitive to face morphing typical artifacts in all regions of a face image is required. We modified our DNN-based detectors by changing the DNN’s structure and the training loss to help the DNN to develop artifact-aware neurons for all regions in der output of the DNN’s feature extractor. These neurons can be exploited by Focused Layer-wise Relevance Propagation (FLRP) to detect traces of forgery in all parts of the image. FLRP is an extension of LRP that we developed to put focus more on detecting class specific regions than on the overall decision of the DNN. FLRP, our modification of the DNN and the new training loss provide in combination an excellent basis for a framework that precisely highlights all traces of forgery in morphed face images. The high accuracy of the morphing artifact localization has been demonstrated in extensive experiments with locally induced traces of forgery. This makes it a perfect tool to highlight suspicious regions in morphed face images to make the detector’s decision more transparent to end-users.
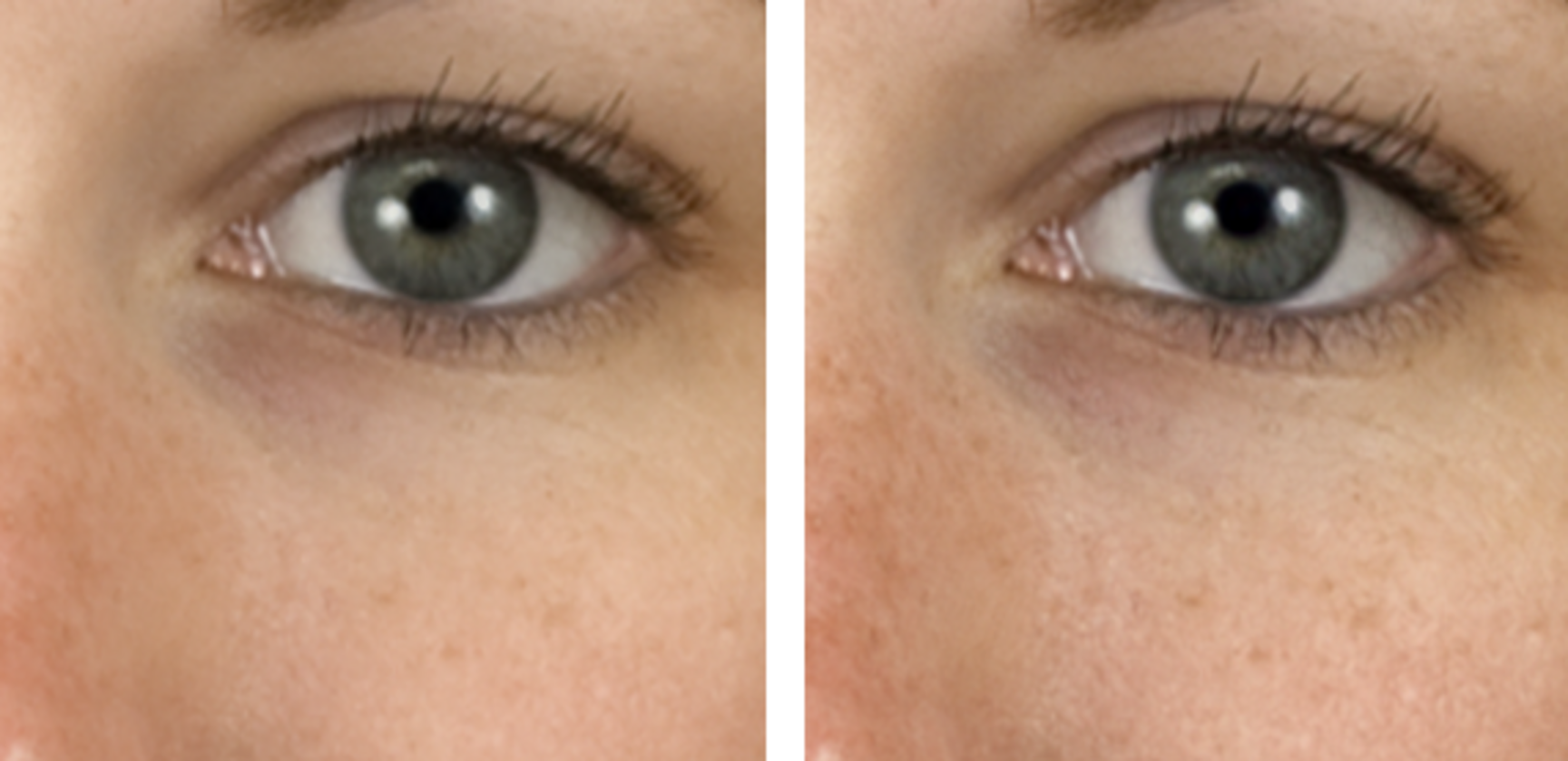
Neural Morph Enhancement
One important step in the process of creating a morphed face image is the blending of two aligned images. During this process, high frequency details, like wrinkles, scars or pore structures are smoothed or get lost and the resulting image appears dull. A detector might use such characteristics to detect morphed faces, but a professional attacker can manually enhance such details to stay undetected. We developed a method based on Neural Style Transfer that counters this image quality degeneration caused by blending. Thus, we are able to generate morphed face images with characteristics similar to the genuine input images. Our detectors were not able to detect such improved images in many cases at first. After adding the improved morphs to our pool of training data, our detectors can reliable detect them too. In addition, our detectors become even better in detecting morphs that have been improved by post-processing methods, which are not reflected by the training data. Improving the face morphs for our training data thus helped to improve the robustness of our detectors against unknown post-processing methods and to develop detectors that are more general.
Robustness Against Image Compression
Face images on the chip of electronic Machine Readable Travel Documents are strongly compressed using JPEG or JP2000 compression methods. We analyzed the effect of these lossy compression methods on the accuracy of different detection methods for morphed face images. We found that our DNN-based detections methods are already very robust against image compression. Our DNN-based methods are still able to detect them, if artifacts, which would be used by a human to classify a face image as a morph, are not recognizable for a human inspector. Further investigations in the intermediate steps of our detectors show that they learned features that are already invariant against compression.
Publications
C. Seibold, A. Hilsmann, P. Eisert
Towards Better Morphed Face Images Without Ghosting Artifacts, Proc. 19th International Conference on Computer Vision Theory and Applications (VISAPP), Feb. 2024 [PDF]
C. Seibold, A. Hilsmann, P. Eisert
Feature Focus: Towards Explainable and Transparent Deep Face Morphing Attack Detectors,
Computers 2021, vol. 10, no. 9, September 2021, doi: https://doi.org/10.3390/computers10090117
C. Seibold, A. Hilsmann, P. Eisert
Focused LRP: Explainable AI for Face Morphing Attack Detection,
IEEE Winter Conference on Applications of Computer Vision Workshops xAI4biom, virtuell, January 2021, doi: 10.1109/WACVW52041.2021.00014
C. Seibold, W. Samek, A. Hilsmann, P. Eisert
Accurate and Robust Neural Networks for Face Morphing Attack Detection,
Journal of Information Security and Applications, vol. 53, August 2020. doi: 10.1016/j.jisa.2020.102526 [Arxiv]
C. Seibold, A. Hilsmann, A. Makrushin, C. Kraetzer, T. Neubert, J. Dittmann, P. Eisert
Visual Feature Space Analyses of Face Morphing Detectors to Predict Generalization Ability,
IEEE Workshop on Information Forensics and Security (WIFS 2019), Delft, Netherlands, December 2019.
C. Seibold, A. Hilsmann, P. Eisert
Style Your Face Morph and Improve Your Face Morphing Attack Detector,
18th International Conference of the Biometrics Special Interest Group (BIOSIG 2019), Darmstadt, Germany, September 2019 [Arxiv] [URL]
A. Makrushin, C. Kraetzer, J. Dittmann, C. Seibold, A. Hilsmann, P. Eisert
Dempster-Shafer Theory for Fusing Face Morphing Detectors,
European Signal Processing Conference (EUSIPCO), A Coruna, Spain, September 2019. 10.23919/EUSIPCO.2019.8902533
C. Seibold, W. Samek, A. Hilsmann, P. Eisert
Detection of Face Morphing Attacks by Deep Learning, Proc. 16th Int. Workshop on Digital Forensics and Watermarking (IWDW2017), Magdeburg, Germany, August 2017. Doi: 10.1007/978-3-319-64185-0_9
S. Lapuschkin, A. Binder, G. Montavon, K.R. Müller, W. Samek
Analyzing classifiers: Fisher vectors and deep neural networks, Proc. Conf. on Computer Vision and Pattern Recognition (CVPR), 2016.